Determining the Assessment Requirement
The CMMC Level 2 process begins with a clear determination of the required assessment type. An organization must establish whether it is subject to a self-assessment or a certification assessment conducted by a C3PAO. This requirement is defined in the contract solicitation through applicable DFARS clauses and is not open to interpretation. Preparing for the wrong assessment path can result in significant rework and may ultimately delay or prevent contract eligibility.
Defining the Assessment Scope
Once the assessment type is confirmed, the organization must define its CMMC Assessment Scope. This step establishes the boundary of what will be evaluated and has a direct impact on cost, complexity, and assessment success. The scope includes all systems and assets that process, store, or transmit Controlled Unclassified Information (CUI), as well as those that provide security protections to those systems. Assets are categorized based on their relationship to CUI, including core CUI assets, security protection assets such as firewalls and identity systems, contractor risk-managed assets that are not fully isolated, specialized assets that may require alternative handling, and assets that are legitimately out of scope. An improperly defined scope—whether too broad or too narrow—can either inflate compliance costs or introduce gaps that will be identified during the assessment.
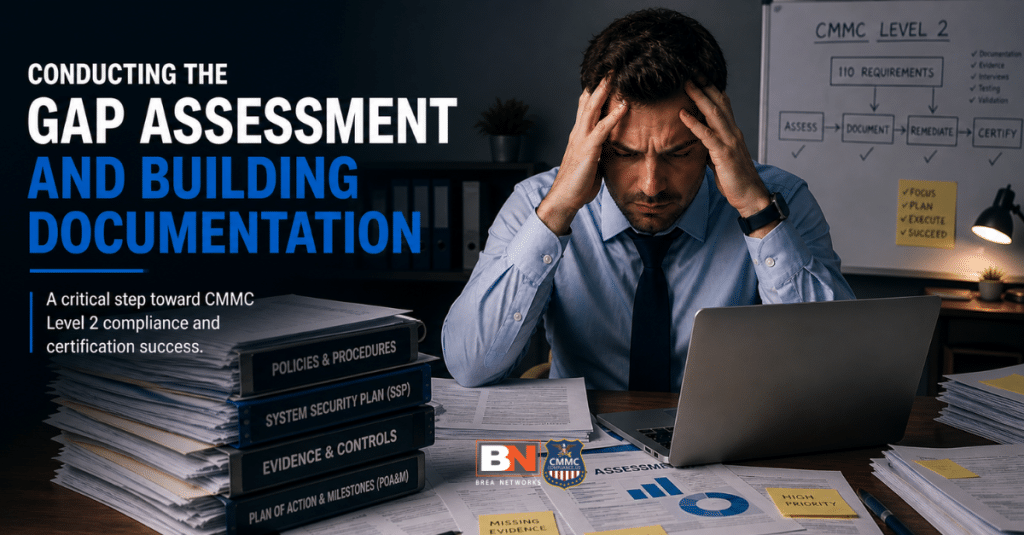
Conducting the Gap Assessment and Building Documentation
With the scope defined, the organization evaluates its environment against the 110 security requirements set forth in NIST SP 800-171. This evaluation mirrors how assessors will later validate compliance, using examination of documentation and configurations, interviews with personnel, and testing of technical controls. The results of this effort are captured in two primary artifacts. The System Security Plan (SSP) documents how each requirement is implemented within the environment, while the Plan of Action and Milestones (POA&M) identifies any deficiencies and outlines how they will be remediated. The POA&M must clearly define corrective actions, responsible parties, and timelines, as it becomes a key input into both the assessment and any conditional certification outcome.
Preparing for the Assessment
Before the formal assessment begins, the organization must complete a rigorous preparation phase. During this stage, documentation is finalized, evidence is organized, and the defined scope is validated against the actual environment. The organization must ensure that its SSP accurately reflects how controls are implemented and that all claims can be supported with verifiable evidence. Pre-assessment coordination activities defined in the CMMC Assessment Process are also completed during this phase. The thoroughness of this preparation directly influences the outcome of the assessment, as deficiencies identified at this stage are significantly easier to correct than those identified during the formal evaluation.

Not sure where your organization stands with CMMC, ITAR, or federal cybersecurity requirements? The fastest way to get clarity is to talk with an expert. Book a call with our team to review your current environment, identify compliance risks, and determine the steps required to move forward. A short conversation can help you avoid costly mistakes and focus on what matters for contract eligibility and security.
SCHEDULE YOUR FREE CONSULTATION!
Executing the C3PAO Assessment
During the assessment, the C3PAO evaluates each of the 110 requirements using three standardized methods: examining documentation and system configurations, interviewing personnel responsible for implementing or managing controls, and testing technical implementations. Each requirement is assessed and scored as either MET or NOT MET. Following the assessment activities, a formal quality assurance review is conducted to ensure accuracy and completeness of the findings before results are finalized.
Determining Assessment Results
The outcome of the assessment is based on the extent to which the organization meets the required security controls. A Final Level 2 certification is granted when all requirements are fully implemented. If the organization meets the minimum threshold for conditional status, it may be granted a Conditional Level 2 certification. This requires achieving at least 80 percent of the total requirements and ensuring that only allowable deficiencies are included in the POA&M. Certain critical requirements are not permitted to be deferred and must be fully implemented prior to certification. If the organization fails to meet the minimum threshold or contains non-permissible deficiencies, certification will not be granted, and a new assessment will be required.
Submitting Results and Issuing Certification
Once the assessment results are finalized, they are submitted to the CMMC instance of the Enterprise Mission Assurance Support Service (eMASS). From there, the results are transmitted to the Supplier Performance Risk System (SPRS), which serves as the authoritative record of the organization’s CMMC status. The organization is issued a Certificate of CMMC Status that documents the achieved level, assessment details, and applicable systems. While the certificate serves as formal documentation, it is the SPRS record that contracting officers and prime contractors rely on when determining eligibility for contract award.
Closing Out the POA&M
If the organization receives a Conditional Level 2 certification, it enters a defined remediation period. All POA&M items must be resolved within 180 days of receiving conditional status. At the end of this period, a POA&M closeout assessment is conducted to verify that all deficiencies have been addressed. If the organization successfully remediates all items, its status is upgraded to Final Level 2. If not, the conditional status expires, and the organization loses its certification, requiring a new assessment to regain eligibility.
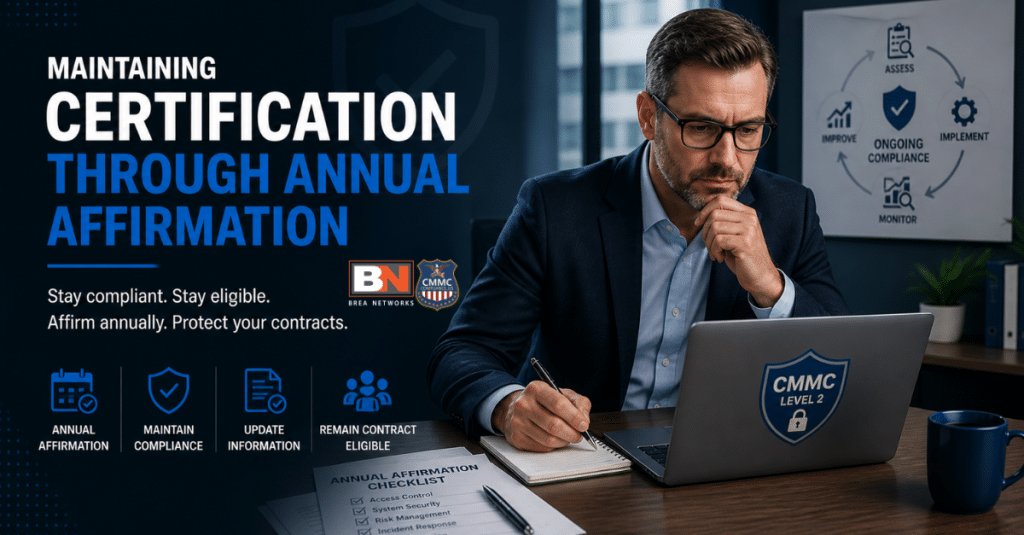
Maintaining Certification Through Annual Affirmation
CMMC Level 2 certification is valid for 3 years, but maintaining it requires ongoing compliance. Each year, a senior official must submit an affirmation in SPRS confirming that the organization continues to meet all requirements within the defined assessment scope. Changes to the environment must remain consistent with the System Security Plan and within the established assessment boundary. Failure to submit the required annual affirmation results in certification lapse, regardless of the original assessment outcome.
The Practical Reality of the Process
Although the CMMC assessment is often treated as a discrete event, it is more accurately understood as a continuous process that begins well before the assessment and continues throughout the certification period. The scope defines the effort required, the evidence determines the outcome, and the timing influences eligibility for contract awards. Organizations that approach CMMC as a one-time audit frequently encounter avoidable failures, while those that manage it as an ongoing operational discipline are better positioned to achieve and maintain certification.

If your organization supports defense contracts and is unsure how CMMC timelines, SPRS requirements, or assessment readiness apply to you, now is the time to get clarity.
About Brea Networks
Brea Networks is a cybersecurity and compliance-focused IT partner dedicated to supporting Defense Industrial Base (DIB) contractors. We help organizations understand and implement the security requirements outlined in FAR 52.204-21, DFARS 252.204-7012, and the CMMC framework. From Level 1 self-assessments to Level 2 readiness and certification preparation, our team works alongside contractors to strengthen system security, define scope, prepare documentation, and build sustainable compliance programs that protect FCI and CUI.