The New Reality of Cyber Threats
Cybersecurity has evolved far beyond a technical concern handled solely by IT departments. Today, it is a core business function that directly impacts revenue, reputation, and long-term viability. For companies operating within the Defense Industrial Base (DIB), the stakes are even higher. These organizations are not just protecting their own data, but also sensitive government information that, if compromised, could have national security implications.
Cyber adversaries are becoming more sophisticated, targeting not only large defense contractors but also small and mid-sized suppliers who may lack mature security programs. These attackers often view smaller organizations as entry points into larger supply chains. The rise in ransomware, phishing campaigns, and supply chain compromises highlights how vulnerable the ecosystem can be when even one link is weak. The Cybersecurity and Infrastructure Security Agency (CISA) continue to warn organizations about the increasing frequency and complexity of these threats, emphasizing the importance of securing supply chains and critical infrastructure. This environment has forced a shift in how cybersecurity is viewed. It is no longer reactive. It must be proactive, continuous, and embedded into every layer of the organization.
What Is CMMC and Why It Matters
The Cybersecurity Maturity Model Certification (CMMC) was developed by the Department of Defense to address exactly these growing concerns. It is designed to ensure that contractors and subcontractors handling Controlled Unclassified Information (CUI) implement adequate cybersecurity practices and, more importantly, that those practices are validated through formal assessments.
CMMC builds upon existing frameworks, particularly NIST Special Publication 800-171, but introduces a critical new element: accountability through verification. Under previous requirements, organizations could self-attest to their compliance. With CMMC, that is no longer sufficient. Companies must demonstrate, through third-party assessments, that their security controls are properly implemented and consistently maintained.
This shift represents a major change in how the DoW evaluates risk across its supply chain. It moves cybersecurity from a checkbox exercise to a measurable and enforceable standard. Organizations that fail to meet these requirements may find themselves ineligible for contract awards, regardless of their technical capabilities or past performance. For more details directly from the Department of Defense, visit:
https://_cio.defense.gov/CMMC/
CMMC is not simply a regulatory requirement. It is a framework designed to strengthen the overall resilience of the defense ecosystem.

Not sure where your organization stands with CMMC, ITAR, or federal cybersecurity requirements? The fastest way to get clarity is to talk with an expert. Book a call with our team to review your current environment, identify compliance risks, and understand what steps are required to move forward. A short conversation can help you avoid costly mistakes and focus on what matters for contract eligibility and security.
SCHEDULE YOUR FREE CONSULTATION!
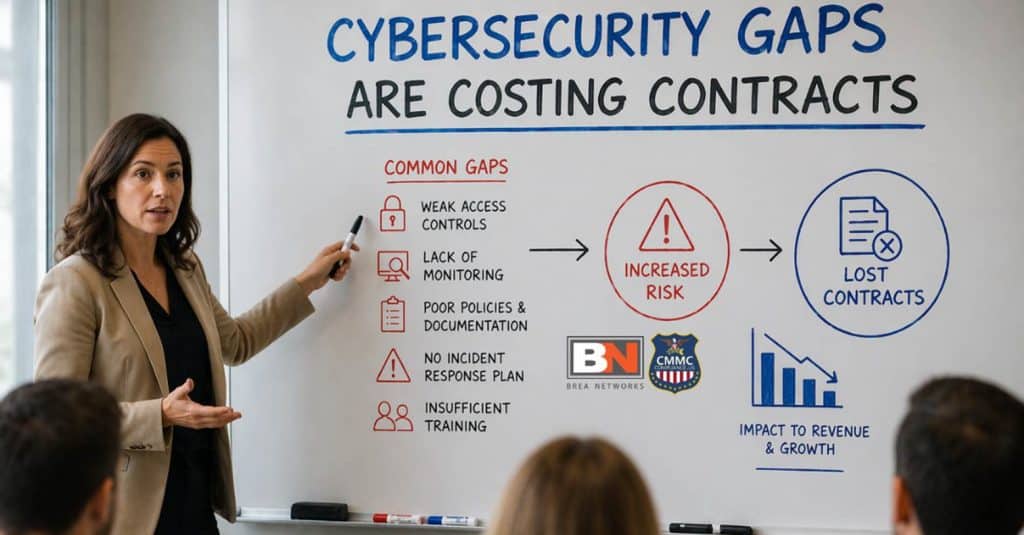
Cybersecurity Gaps Are Costing Contracts
Despite increased awareness, many organizations still operate under the assumption that basic security tools are enough to protect them. While technologies like firewalls, endpoint protection, and multi-factor authentication are essential, they represent only a portion of what is required under modern cybersecurity standards.
The reality is that many companies have significant gaps in their security posture. These gaps often exist in areas such as access control, incident response planning, system monitoring, and documentation. In many cases, organizations may have controls partially implemented but lack the consistency or evidence required to pass an assessment. This creates a false sense of security, where leadership believes they are protected, but in reality, they are exposed.
NIST SP 800-171 outlines the specific controls required to protect CUI, covering everything from risk management to system integrity. These controls are not arbitrary. They are based on real-world threats and are designed to mitigate common attack vectors. Organizations can review the full publication here:
https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-171r2.pdf
Failing to address these requirements does not just increase the risk of a cyber incident. It directly impacts an organization’s ability to compete for and retain government contracts. In today’s environment, cybersecurity maturity is becoming just as important as technical capability or pricing.
CMMC Connects Cybersecurity to Business Growth
While many organizations initially view CMMC as a burden, those that take a strategic approach quickly realize its value as a business enabler. Achieving compliance demonstrates a level of operational maturity that builds trust with prime contractors and government agencies alike. It signals that your organization takes data protection seriously and can handle sensitive information responsibly.
This trust translates into opportunity. As primes become more selective about their supply chains, they are increasingly prioritizing partners who are already aligned with CMMC requirements. Being prepared not only keeps you eligible for contracts but can also differentiate you from competitors who are still struggling to meet the standard.
Beyond contract eligibility, strong cybersecurity practices reduce the likelihood of costly incidents such as data breaches, operational downtime, and reputational damage. In this sense, CMMC is not just about compliance. It is about building a resilient and sustainable business that can operate confidently in a high-risk environment.
Organizations that embrace CMMC early position themselves for long-term success. They move from reacting to requirements to leveraging cybersecurity as a competitive advantage.

The Role of Leadership in Cybersecurity
One of the most critical factors in achieving CMMC compliance is leadership involvement. Cybersecurity cannot succeed as an isolated IT initiative. It requires alignment across the entire organization, starting at the executive level. Leaders must understand that cybersecurity is a strategic priority, not just a technical one.
Executives play a key role in setting the tone, allocating resources, and driving accountability. Without their support, even the most well-designed security programs can fail due to lack of funding, insufficient staffing, or competing priorities. Leadership must actively engage in understanding their organization’s risk exposure, particularly when it comes to handling CUI and meeting contractual requirements.
The NIST Cybersecurity Framework highlights the importance of integrating cybersecurity into organizational risk management processes. It encourages leaders to view cybersecurity as part of overall business strategy rather than a standalone function. More information can be found here:
https://www.nist.gov/cyberframework
When leadership is involved, cybersecurity becomes part of the company culture. It shifts from being a reactive necessity to a proactive discipline that supports growth and stability.
Preparing for CMMC Starts Now
Preparation for CMMC is not something that can be accomplished overnight. It requires a structured approach that includes assessing current capabilities, identifying gaps, implementing controls, and documenting processes. For many organizations, this journey can take months or even longer, depending on their starting point.
Delaying this process can create significant challenges, especially as CMMC requirements begin appearing more frequently in contracts. Companies that wait until the last minute often find themselves scrambling to meet deadlines, which can lead to rushed implementations, higher costs, and increased stress across the organization.
Starting early allows for a more measured and effective approach. It provides time to properly understand requirements, build sustainable processes, and ensure that controls are not only implemented but also operating effectively. It also allows organizations to train their teams and create a culture of security awareness, which is essential for long-term success.
CMMC readiness is not just about passing an assessment. It is about building a security program that can adapt to evolving threats and continue to protect sensitive information over time.
Final Thoughts
Cybersecurity is no longer optional for organizations operating within the Defense Industrial Base. It is a fundamental requirement that directly impacts eligibility for contracts and the ability to compete in a rapidly changing environment. CMMC represents a significant step forward in how the Department of Defense approaches supply chain security, emphasizing accountability, consistency, and real-world effectiveness.
Organizations that take a proactive approach to cybersecurity will be better positioned to navigate these changes. They will not only meet compliance requirements but also build stronger, more resilient businesses capable of withstanding modern cyber threats.
The landscape is shifting, and the expectations are clear. Companies that invest in cybersecurity today are not just protecting their data. They are securing their future.

If your organization supports defense contracts and is unsure how CMMC timelines, SPRS requirements, or assessment readiness apply to you, now is the time to get clarity.
About Brea Networks
Brea Networks is a cybersecurity and compliance-focused IT partner dedicated to supporting Defense Industrial Base (DIB) contractors. We help organizations understand and implement the security requirements outlined in FAR 52.204-21, DFARS 252.204-7012, and the CMMC framework. From Level 1 self-assessments to Level 2 readiness and certification preparation, our team works alongside contractors to strengthen system security, define scope, prepare documentation, and build sustainable compliance programs that protect FCI and CUI.
